Quick Summary
Cryptocurrency mining algorithms are the core component of cryptocurrency mining. If you are learning about cryptocurrency mining, you must be well-versed in mining algorithms, a crucial factor affecting profitability.
In this blog, you will know what a crypto mining algorithm is, its history, purpose, and types. So, let’s dive deep into the topic for a detailed analysis of the crypto mining algorithms.
What is a Cryptocurrency Mining Algorithm?
To produce a valid block, a set of instructions is used, known as cryptocurrency mining. Many mining algorithms are now in use, and each cryptocurrency mining algorithm has advantages and disadvantages.
The SHA-256 algorithm is the first ever algorithm used to mine Bitcoin. Satoshi Nakamoto created Bitcoin to provide security and safeguard the network against unwanted fraudulent attacks.
As cryptocurrencies gained popularity, new algorithms, such as all of the Proof-of-Stake (PoS) algorithms, were developed to reduce the energy demands of proof-of-work (also known as PoW) algorithms.
What is the Purpose of Cryptocurrency Mining Algorithms?
Each mining algorithm has its properties, and these mining algorithms have various purposes to serve and outstanding features such as compatibility of mining hardware, personalized experience, etc.
-
Compatibility of Mining Hardware
The mining algorithms are compatible with their concerned hardware, such as CPUs, GPUs, and ASICs. The compatibility of mining hardware is essential with the specific cryptocurrency chosen to mine. To make sure the results are profitable.
The mining algorithms play a crucial role when the mining hardware minus the cryptocurrency uses the same algorithm explicitly designed for them. It delivers more efficient and profitable results.
For example, ASICs are used in mining bitcoin using the SHA-256 algorithm because it provides efficient results. At first, PCs and CPUs could mine Bitcoins, but the mining results could have been better as the difficulty level increased.
That’s when the ASICs took over due to higher compatibility with the Bitcoin mining algorithm.
-
Personalizing Algorithm
The most lucrative feature of the algorithm is that one can tailor it to the specific needs of the miner. It helps mining enthusiasts to achieve their goals and get their hands on efficient mining for better results.
You can customize the properties of a mining algorithm for power consumption and hash rate. This personalization is often required for more energy-efficient algorithms or for enhancing the memory capacity of the cryptocurrency mining algorithm.
There are mainly two types of crypto mining algorithms: the proof-of-work and proof-of-stake algorithms. Let’s take a broader look at what these two algorithms are:
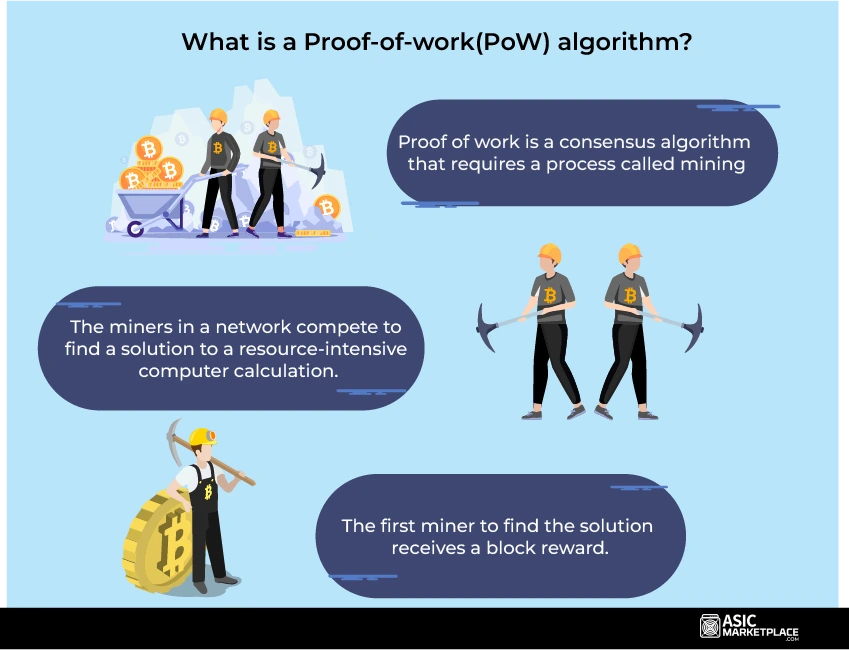
What is a Proof-of-work(PoW) algorithm?
The most popular crypto mining algorithms are proof-of-work (PoW) methods. They demand that miners use processing power to solve challenging mathematical puzzles. The network then validates the answers to these issues, termed “proofs of work,” and rewards the successful miner.
Some of the renowned PoW algorithms are listed below:
- To produce a hash function output with a certain number of leading zeros, the SHA-256 algorithm used by Bitcoin requires miners to find a specific value called a nonce.
- Ethash is ASIC-resistant, making it more available to lone miners.
- ASIC miners are less efficient by introducing Scrypt, which Litecoin employs.
What is a Proof-of-Stake(PoS) algorithm?
An alternate method of mining that emphasizes participant ownership rather than computing power is the Proof-of-Stake (PoS) algorithm. Participants in PoS algorithms can “stake” their digital currency holdings to protect the network’s security and verify transactions. A participant’s stake determines the likelihood of being selected to authenticate a block.
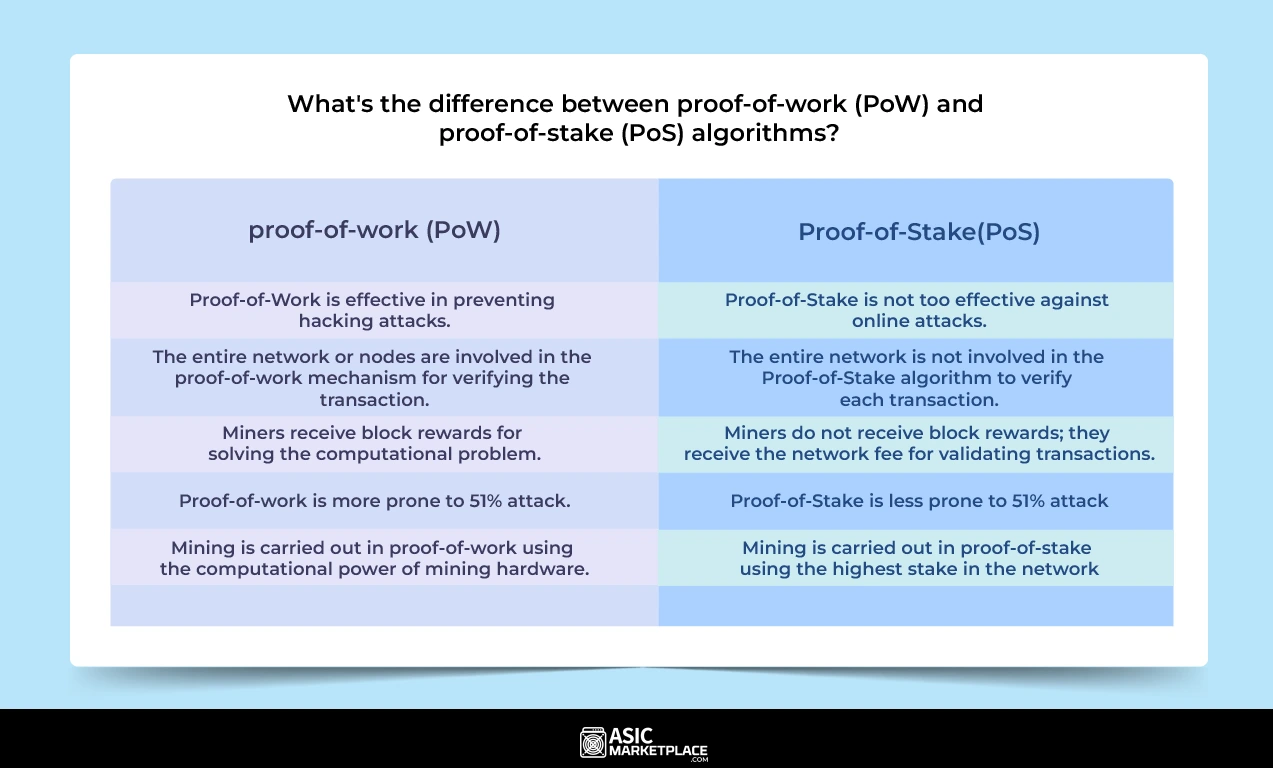
What’s the difference between proof-of-work (PoW) and proof-of-stake (PoS) algorithms?
The difference between the proof-of-work and proof-of-stake is as follows:
The proof-of-work algorithm is used more than the Proof-of-stake due to the above-listed differences. Therefore, a proof-of-work crypto-mining algorithm is a favorable choice for mining worldwide.
How do you choose a suitable mining algorithm for your mining operation?
1. Compatibility
Ensure that the cryptocurrency mining algorithm is compatible with the mining hardware you use to mine the desired cryptocurrency.
2. Profitability
Research the potential profitability of mining with a specific algorithm. Factors like coin value, block rewards, and difficulty level can impact earnings. Consider using mining calculators to estimate potential returns.
3. Security
Evaluate the safety of the algorithm. Some algorithms are more resistant to attacks and vulnerabilities than others. Look into the history of the cryptocurrency and its algorithm to assess its security track record.
4. Network and Community
Consider the strength of the cryptocurrency’s network and community support. A robust and active community can provide updates and support that may be essential for successful mining.
5. Mining Pools
Consider the availability of mining pools that support your chosen algorithm. Mining pools can provide a steadier income stream and reduce the impact of individual miner fluctuations.
6. Feedback
Research online forums, social media, and news sources to gather input and insights from experienced miners. Their experiences can provide valuable guidance.
What is the impact of mining algorithms on security?
Crypto mining algorithms maintain the security of cryptocurrencies in large part. The power of a cryptocurrency network’s mining algorithm and the number of miners involved in the operation define how secure the network is.
A fast algorithm guarantees that it is computationally and financially impossible for an attacker to take over the web.
Additionally, the mining algorithm influences the network’s potential attack vectors. For instance, some algorithms are vulnerable to a 51% attack, in which the attacker has complete control over the computing resources and can influence the blockchain.
Algorithm upgrades and forks also enhance the blockchain’s network security. The enhancements of algorithms become effective once the level of crypto mining begins to change. Know in the next section how algorithm upgrades or forks impact the cryptocurrencies.
What’s the role of forks or algorithm upgrades in cryptocurrencies?
A fork or algorithm upgrade occurs whenever an association modifies the blockchain’s protocol or fundamental set of guidelines. When this happens, the chain divides, creating a second blockchain traveling in a different direction but with the same history as the original version.
Similar to how adjustments to online protocols make web browsing more efficient over time, most digital currencies have autonomous development teams responsible for making network modifications and enhancements.
Therefore, it occasionally occurs for a fork or algorithm upgrade to increase a cryptocurrency’s security or introduce new features.
However, it’s also viable for a new cryptocurrency’s creators to employ a split to launch entirely new ecosystems and coins.
What is the impact of quantum computing on cryptocurrency mining algorithms?
Quantum computers could drastically alter the current Bitcoin mining industry due to their exponentially increased processing capacity. Traditional mining techniques that rely on challenging cryptographic challenges can be vulnerable to quantum assaults.
Cryptocurrency security may be at risk because of quantum computers’ ease in solving issues that would be impossible for conventional computers to handle. The need for building quantum-resistant algorithms has grown, raising worry among the Bitcoin industry.
The use of upgraded algorithms ensures the continuous safety of blockchain networks, which can withstand quantum machines’ processing power. Using quantum-resistant algorithms will be essential in ensuring the integrity and survival of cryptocurrencies in a changing technical environment as quantum computing develops.
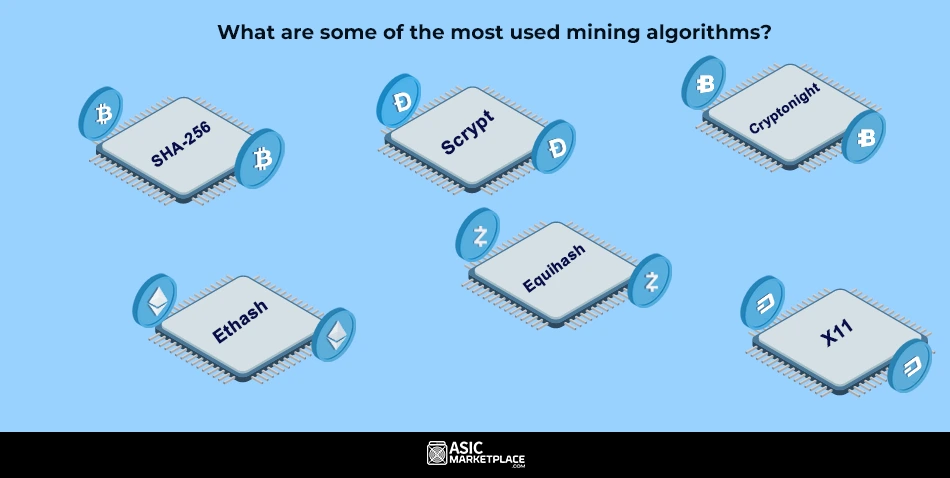
What are some of the most used mining algorithms?
Some of the widely used algorithms are:
1. SHA-256
The National Security Agency (NSA) created SHA-256 on March 5, 2001. It is a hash function for a cryptographic key that is both highly computational and secure against assaults.
Based on the mining difficulty level, the miners compete using the SHA-256 crypto-mining algorithm to find a hash value below a specific target. The first miner who discovers a hash below the goal receives the block reward.
Due to its wide usage and ASIC (Application-Specific Integrated Circuit) improvement, SHA-256 is a very effective algorithm for mining bitcoins.
Features of SHA-256 Algorithm
Its main traits which make it a good option for miners include:
- It is message length and digest length.
- Its irreversible property is a preferred technique for ensuring no alterations in the network.
- Digital signature verification.
- Password encryption.
- SSL handshake in browsing.
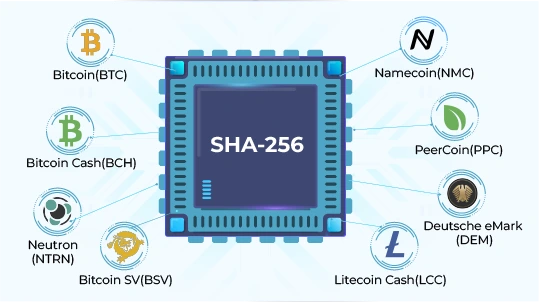
Minable Coins with SHA-256
The list of some top minable coins with SHA-256 includes Bitcoin(BTC), Bitcoin Cash(BCH), Bitcoin SV(BSV), Namecoin(NMC), PeerCoin(PPC), Litecoin Cash(LCC), Deutsche eMark (DEM) and Neutron(NTRN).
2. Ethash
Ethash, a Proof-of-Work hashing algorithm, is used by Ethereum. It shares characteristics with other algorithms like SHA-256 and script in that it needs a lot of memory and processing power to run.
The primary motivation for the development of Ethash was to produce a mining algorithm that forbids Application Specific Integrated Circuits (ASICs). Ethereum’s creators did this to ensure no single party would control more than 51% of the mining power, which can prevent attacks on the network.
The Ethereum blockchain is the one that the Ethash mining algorithm primarily uses. It is where the algorithm now stands after being developed for this project. Because it is a hard fork of Ethereum, the Ethereum Classic project has continued to run on this algorithm.
Features of Ethash Algorithm
Some of the remarkable characteristics of the Ethash algorithm are:
- Its reliance on RAM operations.
- High bandwidth consumption.
- GPU friendliness and great thin client support.
Minable Coins with Ethash
The list of some top minable coins with Ethash includes Ethereum Classic(ETC), Ubiq(UBQ), Expanse(EXP).
3. Scrypt
The scrypt algorithm cryptocurrencies authenticate using password and proof-of-work algorithms. Scrypt is a PBKDF (password-based essential generation function) with solid password security.
Its creation provides critical support to systems that use passwords for identification. It uses complex hashing, the primary hash function, and cryptographic hash methods.
Features of Scrypt Algorithm
It has the following exceptional qualities:
- It is way more sophisticated than other mining algorithms.
- It is energy efficient and uses significantly less energy, which makes it a friendly mining algorithm.
- Scrypt algorithm crypto blockchains have reduced transaction fees.
- Mining Scrypt is substantially quicker than mining Bitcoin.
- Excellent method for securing files, login credentials, and wallets.
Minable coins with Scrypt
Some commonly scrypt mining algorithms employed by cryptocurrencies include Dogecoin(DOGE), Litecoin(LTC), (NYC), PUTinCoin(PUT), HempCoin(THC), Goldcoin(GLC) and LiteDoge(LDOGE).
4. Equihash
Alex Biryukov and Dmitry Khovratovich invented the Proof of Work algorithm Equihash in 2016. It is memory-oriented. The memory response time of Equihash, a memory-bound Proof-of-Work algorithm, is valued above computing power.
This strategy favours GPU mining and renders Equihash ASIC-resistant. Among the cryptocurrencies that employ the Equihash algorithm are Zcash and Komodo.
The memory difficulty of the method guarantees a level playing field for miners and promotes a more equitable division of mining power.
Features of Equihash Algorithm
The features of Equihash that distinguish it from other algorithms are as follows:
- It is an algorithm that aims to prevent the centralized control of mining.
- It offers a difficult cryptographic test to construct but one with low resolution.
- The test requires a lot of storage, and even with adjustments, mining with CPU, GPU, and ASIC always incurs a high cost.
- With greater adaptability, it supports upcoming structural and algorithmic changes.
Minable coins with Equihash
Some of the top coins that are compatible with the Equihash algorithm include Zcash(ZEC), Komodo(KMD), Zclassic(ZCL), Hush(HUSH), and Zero(ZER).
5. Cryptonight
An ASIC-resistant algorithm called Cryptonight encourages transactions focused on privacy and offers fair mining opportunities.
Cryptonight evens the playing field for CPU and GPU miners by introducing different adjustments, such as memory-intensive procedures and random data access patterns.
Cryptocurrencies like Monero and Bytecoin use the Cryptonight algorithm to guarantee an equitable and open mining environment.
Features of CryptoNight Algorithm
A few outstanding qualities of Cryptonight include the following:
- Its ability to be customized, which enables optimization.
- Its high level of encryption has tremendous security.
- CryptoNight manages information to mine blocks and has a modest size for its cryptographic test results compared to the amount of security offered.
- It allows for the creation of entirely non-traceable transactions.
Minable coins with Cryptonight
The coins that one can mine using Cryptonight are Bytecoin(BCN), Swap(XWP), Citadel(CTL), Dashcoin(DSH), and Karbo(KRB).
6. X11
The sequential hashing technique used by the X11 algorithm initially introduced by Dash (previously Darkcoin) uses numerous hash functions.
This strategy lowers energy use and heat production while enhancing security. X11 has grown in popularity among miners searching for lower energy use and higher capacity for ASIC mining because it combines eleven different hashing functions.
Features of X11 Algorithm
A few of the outstanding features that X11 delivers to consumers are:
- More significant amounts of encryption compared to alternative hash methods like SHA-256 or Scrypt.
- As difficult as writing a new hash function could be, X11 programming is not.
- Concerning computational capacity, X11 is much friendlier and more straightforward to resolve.
- The X11 allows modifications to use different hash functions instead of the 11 already established ones.
Minable Coins with X11
The X11 mining algorithm is compatible with the cryptocurrencies Dash(DASH), NativeCoin(N8V), Bolivarcoin(BOLI), BitSend(BSD), Marscoin(MARS), Memetic/PepeCoin(MEME) and Pinkcoin(PINK).
Which is the most Powerful Mining Algorithm?
SHA-256 is the most potent mining algorithm of all. It is due to its greater efficiency in delivering the best output and enhanced decentralized nature that makes it the most favorable one. Everyone uses it, be it people in the government sector or the private sector.
There are plenty of reasons why the SHA-256 algorithm is the top priority of the miners:
It is a one-way algorithm that makes it difficult for attackers to hack the network and keep an eye on the inputs based on the output delivered.
Even the most minor alteration would lead to a drastic change, which strengthens the network’s security, making it all the more difficult for the hacker to manipulate the data. It is most commonly known as the avalanche effect.
It is highly resistant to collision, which secures the authentication of the transactions, leading to a more secure blockchain network.
Bitcoin mining with SHA-256
The critical operating component in Bitcoin’s mining process is the SHA256 algorithm, whose difficulty is now very high and steadily rising. The SHA-256 secures the Bitcoin network and maintains its immutability.
ASICs are specially designed mining hardware for Bitcoin that deliver more significant outputs. ASIC Mining hardware, Bitcoin, and SHA-256 are the best combination, marking a more secure and efficient mining.
It developed the interest of mining enthusiasts worldwide, leading to an increased Bitcoin mining difficulty.
Bitcoin Mining Difficulty Chart
Source: Coinwarz
The chart depicts the mining difficulty data for the last six months, which has increased clearly over time. The current Bitcoin Difficulty is 57.32T.
Conclusion
The algorithms used in Bitcoin mining are essential to the process. These are crucial since they affect the blockchain network’s hash rate, effectiveness, and security. The Proof-of-Work and Proof-of-Stake algorithms are just two examples of the various mining algorithms divided into two categories.
You are knowledgeable about cryptocurrency algorithms because we covered everything, and now is the time when you can put the knowledge to use by applying it.
Check out the latest SHA-256 ASIC Miners 
Check Now 
FAQs on Crypto Mining Algorithms
-
What are the two main consensus algorithms involved in cryptocurrency mining?
The two main consensuses are algorithms involved in cryptocurrency, mining of proof of work, and proof of stake.
-
How does the mining algorithm secure the network?
The power of the cryptocurrency mining algorithm and the number of enthusiasts involved in cryptocurrency mining is what sets the network secure.
-
Which mining algorithms are primarily in use?
The mining algorithms primarily used are SHA-256, Scrypt, Ethash, Equishash, X11, and Cryptonight.
Peter Davis is an accomplished blockchain analyst and technical writer with over four years of experience in the cryptocurrency sector. His expertise spans blockchain infrastructure, ASIC mining hardware, and digital asset markets, where he is recognized for translating complex technical concepts into precise, insightful, and accessible analysis for a global audience.
With a strong foundation in technical research and market evaluation, Peter’s work focuses on bridging blockchain innovation with practical mining and investment strategies. His writing is defined by analytical depth, clarity, and a focus on data-backed insights that guide both professionals and enthusiasts through the evolving crypto landscape.
Driven by a deep passion for Web3 technology and decentralized systems, Peter continues to produce authoritative, research-driven content that enhances understanding of ASIC mining performance, blockchain efficiency, and the broader dynamics shaping the future of digital finance